The First Open-Source War


Welcome to the first open-source war. You’ll find your news channels through TikTok footage, updates through independent news sources, quotes from Twitter commentators, and visualize the movement of destruction through a geographic stitching of public records.
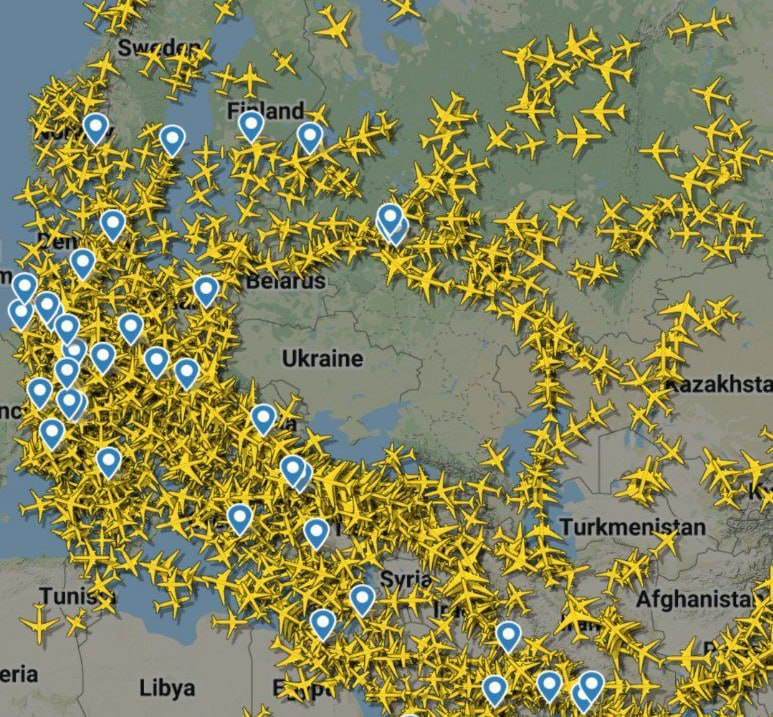
There aren’t any push requests or issue tracking systems per se as contributions are all instantly updated, propagated, and cross-examined. So, what’s this mean for you and me? From what we’ve seen with Russia’s invasion of Ukraine, we get fragmented, hyper-personal, and brutal snapshots of the conflict in real-time. We piece together the latest events from an assortment of sources and media types. Interestingly, the latest of these media types is independently collected flight data showing the “negative space of war.”
Contrary to my early education’s disapproval of Wikipedia, I still use the online compendium as a jumping off spot for research. And if you’re like me, you’ve probably never explored the “Talk” tab available on any Wikipedia article. Navigating to the Talk tab on the “2022 Russian invasion of Ukraine,” we can witness the brisling battle between Wikipedia editors. Debates range from the particulars of what defines a battle to the removal of political bias in location names and calculating collateral damage. This tab makes researching no longer like reading about history, and instead more like watching history write itself. For me personally, it gave me a much greater appreciation for how fast information can transform from being deemed “fact” to “misinformation.” As of writing this, the last edit for the invasion was 29 seconds ago.
All of this gives us a more comprehensive and nuanced understanding of war’s impact on humanity. This is precisely what happens when Open-Source Intelligence (OSINT) becomes the norm. With the invasion of Ukraine, we’re getting to see OSINT in action. Because “President Vladimir Putin, a former KGB agent, is obsessed with disinformation and false-flag operations,” says American tech journalist Mike Elgan, “OSINT is the strongest and fastest method we have for disproving false-flag disinformation.”
Take Tass, a Russian news agency, and their emergency report published on February 21st. In it, they claimed that:“A Federal Security Service (FSB) border security unit detected an infiltration of the border with the Republic of Ukraine by a sabotage group…Five violators of the Russian Federation borders from the sabotage group were eliminated in the ensuing combat.”
As soon as helmet-cam footage of the skirmish was released, Twitter quickly took to breaking down the claims piece by piece.
The have now released "helmet cam" footage for the claimed incursion by Ukrainian troops.
— Oliver Alexander (@OAlexanderDK) February 21, 2022
Because if you are going sneak into Russia to perform sabotage, you of course bring a helmet cam and BTRs. pic.twitter.com/6r7k6kYzLI
One particular Twitter user examined the video’s metadata and compared it to satellite imagery of the skirmish’s location. From that cross-examination, he realized that it was the same location that Russia had claimed had been the spot of artillery firing.
This is exactly the same spot https://t.co/c0rr92wgET
— Your Inner Beauty (@lambdadmitry) February 21, 2022
So they not just took helmet cams and an APC, but also decided to go in at exactly the same spot they supposedly shelled (singular) a day before that, supposedly full of investigators https://t.co/R9blcsaAMb pic.twitter.com/kSveriVrIV
In actuality, it was found that the helmet-cam video was taken “inside separatist territory right on the border with Russia. This appears to be yet another fabricated videos for another false flag [sic].” Free and independent fact-checking is the name of the game.
But besides becoming better informed and severing the spread of fake news, does OSINT offer any other offensive plays? Yes, it absolutely does. On Friday morning, I woke up to a flurry of Discord messages discussing a link that allows visitors to shut down Russian government sites. Distributed Denial of Service (DDoS) is a cyber-attack strategy that causes websites to go offline by overloading them with requests. You can think of it as a casual game of catch with your dad suddenly turning into a violent, 100-person game of dodgeball with you as the only target. Accessing this link makes you one of the people hurling fastballs at Russian disinformation sources. Genius and very effective. As a disclaimer, if you decide to visit the site, please go incognito and use a VPN.
open this site and leave it running in your browser to basically loop requests to overload certain russian news portals: https://t.co/gKnTgVitbL guys at work checked the code, it does exactly what it says and isn't malicious (to the user).
— kod 🧪💾 @ Lost Ark probably (@kod_exe) February 25, 2022
We’re living in an unthinkably complex and interconnected world. While these dynamics make tragedies like the Russian and Ukrainian conflict impenetrable and confusing, we can have tremendous solace that technologies, customs, and strategies are being developed and employed as we speak. And thankfully, they’re often authored not by secretive organizations or political parties but by real people like you and me.



